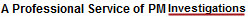
Intrusion Log Collection Process
Collecting the logs from any computer system or digital device must be done to ensure the accuracy of the information in the event the case either goes to law enforcement or you plan to file a law suit.
In the above collection diagram, you can see the steps needed to properly collect log files. Although you can skip the password protection level, its very important to document why you decided not to password protect the logs you collected. In addition, should the logs be provided to an outside independent intrusion specialist, a proper chain of custody needs to be established.